Wow. I suppose it shouldn’t be surprising, but I spent much of last evening working through the big-picture details surrounding the emails alleged to have been between L.J. Bryant and the webmaster for (the now defunct) greedymontydavenport.com. Not long after that initial post, I had something of an epiphany, and I emailed a number of friends who are the types of people that tend to know the answers to technological questions. I also, with the help of another friend, was able to get a professional background researcher to do some digging on all of this. (As of this writing, I am waiting to hear back from the researcher.)
Wow. I suppose it shouldn’t be surprising, but I spent much of last evening working through the big-picture details surrounding the emails alleged to have been between L.J. Bryant and the webmaster for (the now defunct) greedymontydavenport.com. Not long after that initial post, I had something of an epiphany, and I emailed a number of friends who are the types of people that tend to know the answers to technological questions. I also, with the help of another friend, was able to get a professional background researcher to do some digging on all of this. (As of this writing, I am waiting to hear back from the researcher.)
Point being, I spent the better part of my Tuesday afternoon/evening trying to get a whole lot of e-ducks in a row so that I could attempt to opine intelligently on the issues.
We initially ran the emails because we figured they were going to come out one way or another, and we guessed (correctly, it seems) that too many other outlets would take them at face value rather than try to get to the truth, so we wanted to keep eyes here as much as possible in the event that we uncovered something. Unfortunately, this thing has unfolded like the movie Primer; the further I dug into the whole mess to try and get at the truth, the more confusing some of the details became.
For example, the email I received from greedymonty@greedymontydavenport.com in reply to my May 6, 2010 message was sent from ip address 199.200.27.7, which is registered to Fidelity Information Services, Inc., on Rodney Parham Road in Little Rock.

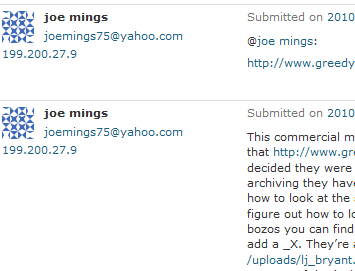
OK, whatever. But, wait… what’s this? The ip address of “joe mings” comment that prompted this whole thing was 199.200.27.9, which is also registered to Fidelity Information Services, Inc.
That’s right — the guy who registered the URL anonymously and who used a pseudonym (or nom de blogge, if you prefer) to correspond with inquiring emailers was apparently the same guy who then “broke” the story about the emails being visible to all the world. (If it wasn’t the same guy, it was someone right there in the same building, which is either pretty much the same thing or the biggest coincidence ever.)
So, ever the intrepid seeker of truth, I emailed both greedymonty@greedymontydavenport.com and joemings75@yahoo.com.
As I’ve investigated this whole email thing a little further, I’ve realized something rather important — the emails I’ve received from greedymonty and the comment posted by joe mings came from nearly identical IP addresses that were definitely within the same company. So what’s the deal?
I don’t have a dog in this fight, really. If the emails are legit, I want to report them as such. If they aren’t, then I want to figure out who is behind them. The easiest way to settle this that I can see is for greedymonty@greedymontydavenport.com to forward (not cut-and-paste) the emails in question to me so that I can verify.
–Matt
Less than one minute after sending my email, I received:
Delivery to the following recipient failed permanently:
greedymonty@greedymontydavenport.com
Technical details of permanent failure:
Google tried to deliver your message, but it was rejected by the recipient domain. We recommend contacting the other email provider for further information about the cause of this error. The error that the other server returned was: 550 550 #5.1.0 Address rejected greedymonty@greedymontydavenport.com (state 14).
and
Delivery to the following recipient failed permanently:
joemings75@yahoo.com
Technical details of permanent failure:
Google tried to deliver your message, but it was rejected by the recipient domain. We recommend contacting the other email provider for further information about the cause of this error. The error that the other server returned was: 554 554 delivery error: dd This user doesn’t have a yahoo.comaccount (joemings75@yahoo.com) [-5] – mta1089.mail.sk1.yahoo.com (state 18).
Yep, the listed email address for the URL was no longer active and the Yahoo! address for the person who broke the story never even existed.
Speaking of “joe mings” and his infamous comment, let’s unpack it a bit.
I don’t know what digging you did to find out who they were when you decided they were just regular citizens but the guy that runs it is working for Bryant.
The only “proof” of this is, of course, the aforementioned emails. However, as Kurt correctly noted in this comment, the lack of any header information in what purports to be archived (read: NOT cut-and-pasted copies of) messages is highly suspicious at best.
I’m not sure what sort of mail archiving they have turned on but all the received e-mail is stored in the uploads folder under the website.
Read that again. The mail is stored in the uploads folder? How would that make any sense at all?
Answer: It doesn’t. I’ve bought three different domains through GoDaddy, Inc., in the past, and never, ever has the default for mail storage been to place them as unencrypted text files in a publicly visible uploads folder. So, for the messages to be in that folder, the person running the site would have to somehow change a number of settings and intentionally place them there. Yet here you have someone who registered the URL anonymously and has tried avoid giving out any information that would identify the person(s) behind the site; we’re supposed to believe that, despite this, he would make a concerted effort to make the emails visible?
If you know how to look at the site in a folder structure, it’s easy enough to find. They’re not even encrypting it.
As mentioned, www.greedymontydavenport.com was purchased through GoDaddy. I’ve bought a couple different domains in the past from them, so I decided to look at the folder structure of one of those sites. Know what I found? NO publicly visible emails. And here’s a look at my “uploads” folder.
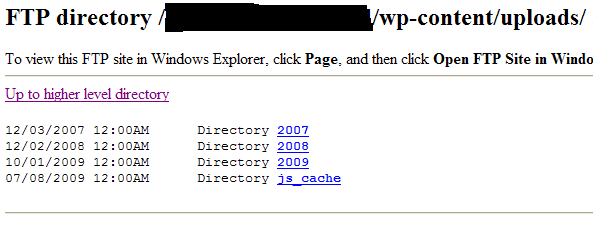 See any emails?
See any emails?
Even if you can’t figure out how to look at the folder structure, if you know the e-mail address of someone that’s sent an e-mail to those bozos you can find it without even trying. You just have to replace the @ in the e-mail address with an _ and then just add a _X. They’re all in unencrypted text files. For instance, just paste http://www.greedymontydavenport.com/uploads/lj_ljbryant.com_1.txt and keep changing the number and you’ll see everything he’s sent.
I thought I’d test this theory. After all, I knew that I’d sent three emails to that website. So I followed the instructions and plugged in my info. Result?
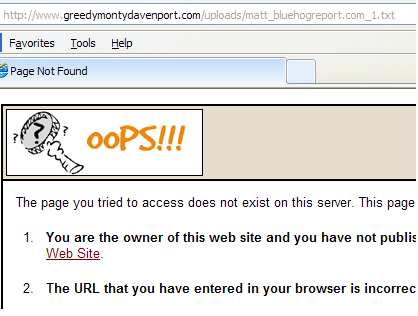 Translation: The idea that every single email is archived automatically in that folder? Untrue.
Translation: The idea that every single email is archived automatically in that folder? Untrue.
What a buch [sic] of morons. If that’s the group claiming to want to bring technical modernization to Arkansas and that’s the best they can do for security, I’m scared for the future.
ANYWAY…
These results are unsurprising according to the three different IT pros I spoke to last night. Not one of them had ever seen or even heard of an email server that would auto-archive in such a silly manner. So, just to triple-check things, I emailed GoDaddy and asked. Their response:
Dear Matt,
Thank you for contacting Online Support.
The issue you have described is something that our mail servers would not do as they do not deliver email to a hosting account. Therefore, it does appear like a fake issue. If there is more detailed information on the situation that you can provide we’d be happy to look into the matter further. Information we would need for sure would be the hosting account in question and the four digit support PIN for the account that has the hosting account. The email you received would also be beneficial.
Please let us know if we can help you in any other way.
Sincerely,
Jason P
Online Support Representative
But what about the emails, then? After all, the email that quoted me was real and unchanged, a fact that, when combined with the fact that greedymonty and joe mings sent their correspondence from the same office, more or less establishes that the person(s) running the website were the same ones who uploaded these text files. But does that mean that the messages allegedly from Bryant are similarly legit cut-and-pastes of actual emails?
Well, while I cannot say for sure, it’s worth noting that there are several inconsistencies in the emails. To wit:
- The author generally uses “To: LJ Bryant” and “From: LJ Bryant <lj@ljbryant.com>” in the headers. However, in the emails dated May 7 and May 9, the headers only say “From: LJ Bryant” without the address. Emails from dates on either side of these (5/4, 5/6, 5/8, and 5/16) all use the form that contains “<lj@ljbryant.com>.” The emails I’ve received from greedymonty always show “From: Matt .”
- Similarly, where an email purported to come from Bryant contains the quoted message from greedymonty, the header is generally in the form of “From: greedymonty@greedymontydavenport.com [mailto: greedymonty@greedymontydavenport.com].” In the emails from 4/11 and 4/19, the bracketed “mailto” address is missing.
- The emails that I numbered 13 and 14 seem to have a half-finished duplicate email (bolded) and one of them is clearly missing a recipient address.
Subject: RE: And the hate mail starts From: LJ Bryant Date: Sun, May 09, 2010 10:55 pm To: I just really want to win this election and I’ve spent a lot of money that I don’t want to see flushed down the tubes. From: greedymonty@greedymontydavenport.com [mailto:greedymonty@greedymontydavenport.com] Sent: Sun, May 09, 2010 11:11 am To: LJ Bryant Subject: RE: And the hate mail starts Yeah, yeah. I know. You worry to much. Subject: RE: And the hate mail starts From: LJ Bryant Date: Sat, May 08, 2010 9:00 pm To: Thanks. Please make sure that you don’t tip them off that we’re affiliated. Subject: RE: And the hate mail starts From: LJ Bryant <lj@ljbryant.com> Date: Sat, May 08, 2010 9:00 pm To: <greedymonty@greedymontydavenport.com> Thanks. Please make sure that you don’t tip them off that we’re affiliated.
- Where the alleged email from Bryant contains the quoted original message from greedymonty, the placement of the “Subject” line in the original messages varies, appear before the “From” sometimes and after the “To” at other times. (See email from 4/8 and 4/19 for comparison.) Based on the emails I’ve received from the address, the Subject before the From line is the way his email does it by default.
- A little more tenuous, I admit, but the email dated 5/7 has Bryant saying “Okay…leave it up.” At no other point in any of these emails does Bryant use an ellipsis. If your friends are anything like mine, the ones who use ellipses, use them fairly often. greedymonty uses an ellipsis in his hypothetical reply to Wickline, however.
I am attempting to find out who registered the website, and I will update this post if/when I find out. For now, though, I see six plausible scenarios:
1. The emails are legit, but the people who run greedymontydavenport.com got mad at Bryant for some reason and uploaded those emails to ruin him.
2. The emails are legit, but someone (who coincidentally worked in the same office as the site’s webmaster) hacked the domain, found the emails, and uploaded them.
3. The emails are legit, and Bryant had them leaked so that he could play innocent and make it look like someone was trying to ruin him because they were afraid he would win.
4. The emails are legit, and the people who run the website were working as double agents for Davenport the whole time and are now trying to make Bryant look bad for going negative.
5. The emails are fake, but the person the people who run the website were working for Davenport the whole time to try and make Bryant look bad, and the created emails are just taking the subterfuge a little further.
6. The emails are fake, but the person (whether attached to Davenport or not) running the site knew that Wickline and I would see our authentic emails and would believe that the rest were legit, too.
None of these theories is perfect, of course. Half require Bryant to be some kind of postmodern Keyser Soze, a couple require Monty Davenport to have rolled the dice on doing an anti-Davenport site long before Bryant was a factor in the race, etc. That said, there are certainly enough questions surrounding the emails that I am uncomfortable saying that I think Bryant actually sent them. (Kurt raises a couple other questions here, too.) Could they be legit? Sure. But they could just as easily and as likely be fake. Until we have something more concrete than all of this, I am going to have to assume that they are not real, and I am still happy to cast my vote for L.J. Bryant.
I thank everyone who has helped so far in researching this issue. I have a feeling this won’t be the last we hear of it.